![]() One management tool for all smartphones to transfer files between PC & iOS/Android devices.
One management tool for all smartphones to transfer files between PC & iOS/Android devices.
The FBI announced Monday that it managed to unlock an iPhone 5c belonging to one of the San Bernardino shooters without the help of Apple. Some news outlets citing anonymous sources have identified Israeli police technology maker Cellebrite -the provider of mobile forensic software, as the undisclosed third party helping the government. However, neither the FBI nor Cellebrite has officially commented on their contract publicly.
Now the question of millions of Apple users is: How the Mobile Forensic software works? Does this make your phone less private?
Here we compares Cellebrite Mobile Forensic with its competing products - Micro Systemation XRY and Syncios Data Recovery.
Cellebrite is an Israeli company that manufactures data extraction, transfer and analysis devices for cellular phones and mobile devices. It has two business divisions: the Cellebrite Wireless Carriers & Retailers, which produces hardware and software for phone-to-phone data transfer, backup, mobile applications electronic software distribution, and data analysis tools; and the Cellebrite Mobile Forensics, which is mainly delivered to government or legal organizations, such as federal, state, intelligence agencies; military branches.
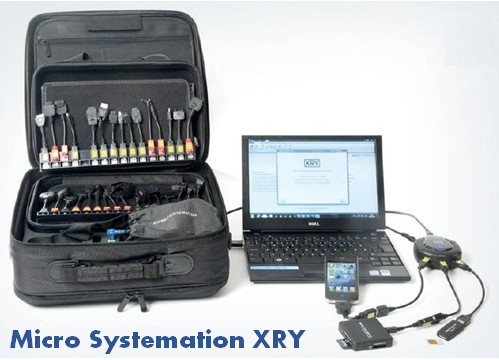
Micro Systemation XRY - the most serious rivalis to Cellebrite, the company writes a forensic system called XRY, specifically designed for analyzing mobile digital devices. The software is designed to run on a Windows computer and will retrieve information from mobile devices for immediate display of the results or files can be saved for later analysis.
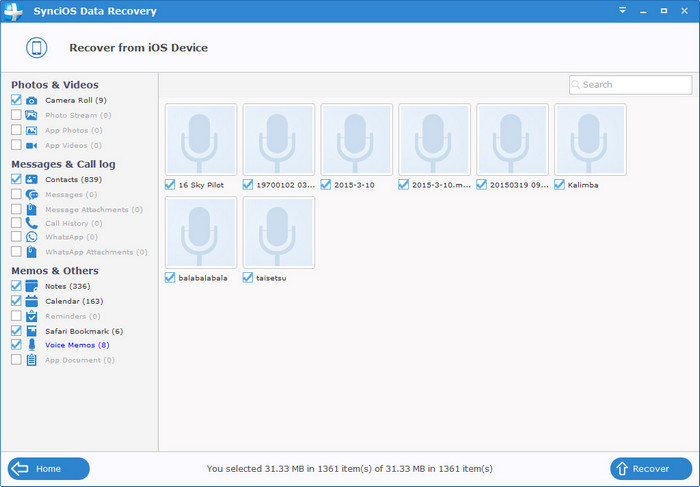
The Syncios iOS Data Recovery, is also an data extraction, transfer and analysis tool for iOS devices. The software is developed by Anvsoft Inc, which is an Chinese company established in 2002. Simally to the Cellebrite, it has another product brunches phone-to-phone data transfer, data-backup and mobile manager.

Cellebrite is really powerful, allowing for physical, logical, user password and file system extractions, data extraction of existing, hidden and deleted data, decipher lock codes and access and decode internal application data including: International Mobile Subscriber Identity (IMSI) history, past SIM cards used, user lock-code history and more
The XRY can grab phone book information, SMS and other text messages, MMS, call lists, calendar entries, task items, pictures, media files, and SIM card information. XRY also retrieves a lot of information about the phone itself, such as IMEI/ESN, IMSI, model no., matching between the clock in the telephone and the computer, etc.
The Syncios Data Recovery delivers three recovering mode, allows iOS users to recover and transfer lost data from iPhone/iPad/iPod, iTunes and iCloud. It supports recovering up to 16 types of data, including notes, SMS, whatsApp messages, pictures, call logs, contacts, voce memos, etc. The software can access to your iDevice's database in some hard circumstances, such as iPhone got broken, crashed, smashed, water damaged; iOS upgrade, jailbreaking failure or factory settings restore on your device.
Though we didn’t go into detail about how Cellebrite is working around the iPhone’s built-in security measures, experts speculate the attack is based on a NAND mirroring technique, which involves essentially copying the flash memory of the device so it can be restored after a lockscreen wipe..
However, according to Dickinson - the firm’s marketing director, XRY works much like the jailbreak hacks that allow users to remove the installation restrictions on their devices. But he wouldn’t say much about the exact security vulnerability that XRY exploits to gain access to the iPhone.
By contrast, the Syncios Data Recovery is base on totally different technical measures. It is noticeable that the program would not recover data that had been overwritten. Besides, since it is individual-oriented, for protecting personal privacy, users have to unlock their handset or login to the Apple their account to authorize the program to read database. In general, your mobile phone data can be guaranteed to be 100% secure.